Logitech Security Breach: Clop Ransomware Attack Details
Logitech, a leading manufacturer of computer accessories and electronic devices, has publicly acknowledged a recent security breach resulting from a cyberattack carried out by the Clop ransomware group. This attack targeted the company's data systems in July, specifically exploiting a vulnerability related to Oracle's E-Business Suite.
The Swiss-based multinational company, renowned for its diverse range of products including peripherals, gaming gear, and smart home devices, took swift action upon discovering the breach. In an official filing with the U.S. Securities and Exchange Commission, Logitech confirmed that some data had been compromised, though it assured that customer products and core operations remain unaffected.
According to Logitech's statement, the breach involved the unauthorized extraction of data, which potentially included limited personal details of employees, consumers, and business partners. Importantly, the company emphasized that sensitive information such as national identification numbers and credit card details were not stored within the compromised systems, and thus were not at risk.
The company attributed the breach to a zero-day vulnerability in a third-party software component. Once the flaw was identified, Logitech promptly applied the necessary security patch to close the vulnerability. The incident was swiftly contained, with external cybersecurity experts engaged to assist in the investigation and response.
The breach became publicly visible when the Clop gang added Logitech to its online leak site last week, releasing nearly 1.8 terabytes of what it claims to be stolen data. Although Logitech did not specify the exact software vendor involved, industry analysts suggest that the attack exploited a previously unknown flaw in Oracle’s software, which the hackers exploited during their July assault.
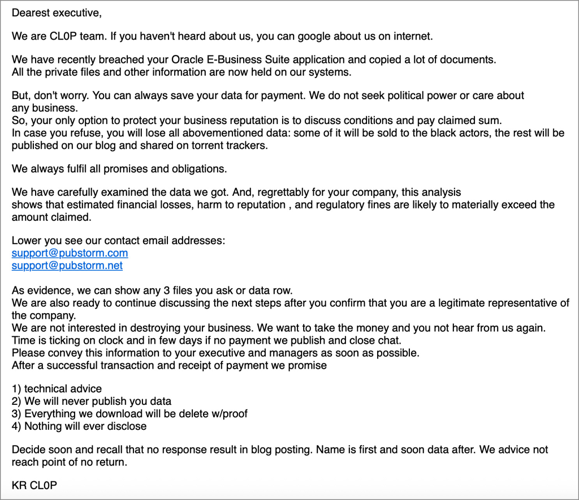
This attack aligns with a broader pattern observed last month, where cybersecurity firms like Mandiant and Google identified a new extortion campaign. In this scheme, multiple organizations received threatening emails from the Clop group, claiming that sensitive data stolen from their Oracle-based systems was to be leaked unless ransoms were paid.
Soon after the incident, Oracle disclosed a critical vulnerability within its E-Business Suite, designated as CVE-2025-61882, prompting the release of an urgent security patch to mitigate the risk. This zero-day flaw has been actively exploited by malicious actors, notably the Clop ransomware group, which has a notable track record of leveraging such vulnerabilities for large-scale data breaches.
Historically, Clop has demonstrated a pattern of targeting zero-day vulnerabilities across various platforms, including the 2020 attack on the Accellion FTA platform that compromised nearly a hundred organizations. In 2021, they exploited a zero-day in SolarWinds Serv-U FTP software. The year 2023 marked several significant breaches: over a hundred companies were affected when Clop exploited a zero-day in the GoAnywhere MFT platform, and their most extensive campaign involved a zero-day in MoveIt Transfer, resulting in data theft from over 2,700 organizations globally.
Additionally, in 2024, Clop exploited two zero-day vulnerabilities in Cargowise's Cleo File Transfer software (CVE-2024-50623 and CVE-2024-55956), leading to widespread data exfiltration and extortion efforts. The recent Oracle breach has impacted notable institutions such as Harvard University, Envoy Air, and The Washington Post.
BleepingComputer reached out to Logitech earlier this month and again today for comments regarding the breach. We will update this report if any responses are received.
Why People Need VPN Services to Unblock Porn
People need VPN services to unblock porn because they often face geo-restrictions, censorship, and privacy concerns that limit access to adult content. Unblock porn through VPNs allows users to bypass regional blocks, protect their browsing anonymity, and enjoy unrestricted access to content that may otherwise be unavailable in their location.
Why Choose SafeShell VPN to Access Adult Content
If you want to access region-restricted content by performing a Porn unblock, you may want to consider the SafeShell VPN for its comprehensive benefits.
- To unblock porn sites, SafeShell VPN utilizes a vast network of global servers, allowing you to bypass geo-blocks and access content from virtually any region with ease.
- It ensures your privacy is maintained through military-grade encryption, keeping your online activities anonymous and secure from ISPs or surveillance.
- The service offers consistently high-speed connections, which is crucial for streaming high-definition video content without frustrating buffering or lag.
- With innovative features like App Mode, you can simultaneously access content libraries from multiple countries without needing to manually switch servers.
- SafeShell VPN supports multiple devices on a single account, providing seamless protection and access across your smartphones, computers, and streaming devices.
How to Use SafeShell VPN to Unlock Porn Sites
To begin using SafeShell VPN to access adult content from any region, start by subscribing to SafeShell VPN through their official website, where you can select a plan that best suits your needs. Once you have completed your subscription, download the SafeShell app compatible with your device and proceed to install it. After installation, open the app and enable the App Mode feature to ensure maximum flexibility and access options during your browsing session.
Next, navigate to the server selection within the app and choose a server location from SafeShell VPN's extensive global network that corresponds to the region where the desired content is accessible. Connecting to this server will mask your real IP address and make it appear as though you are browsing from that specific location. Finally, browse the internet securely and privately, enjoying unrestricted access to content without revealing your true identity, all facilitated by SafeShell VPN's robust privacy protections.
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Oyunlar
- Gardening
- Health
- Home
- Literature
- Music
- Networking
- Other
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness


