Facial Authentication Strengthening Identity Verification and Workplace Security
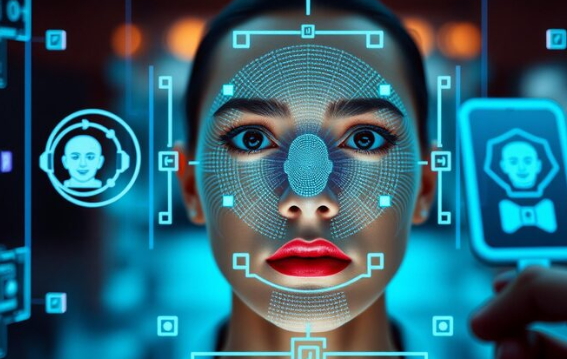
As businesses continue to adopt digital technologies, securing access to systems and sensitive data has become more critical than ever. Traditional passwords and PINs are no longer sufficient to protect against modern cyber threats. This is where Facial Authentication emerges as a powerful solution, offering secure and convenient identity verification.
By using advanced biometric technology, facial authentication allows organizations to confirm a user’s identity quickly and accurately. From unlocking devices to securing enterprise applications, this technology is transforming how companies protect digital assets and prevent unauthorized access.
What Is Facial Authentication?
Facial Authentication is a biometric security method that verifies a person’s identity using unique facial features. A camera captures an image of the user’s face, and the system analyzes key facial points such as the eyes, nose, and jawline to create a digital template.
The process usually includes:
-
Capturing a facial image through a device camera
-
Mapping unique facial landmarks
-
Converting the data into a biometric template
-
Comparing it with stored records for verification
Because every face has unique characteristics, facial authentication offers a reliable and contactless method for secure access.
Key Benefits of Facial Authentication Technology
Organizations across industries are adopting Facial Authentication because it combines security, convenience, and efficiency.
Major benefits include:
-
Enhanced security: Difficult to replicate or steal compared to passwords
-
Fast verification: Authentication happens within seconds
-
Contactless access: Ideal for modern workplaces and remote teams
-
Reduced credential theft: Eliminates risks of password sharing
-
Improved user experience: Employees access systems quickly without remembering complex credentials
These benefits make facial authentication particularly useful in high-security environments.
Facial Authentication and Modern Cybersecurity Strategies
Cybersecurity threats continue to evolve, especially in distributed work environments. Integrating Facial Authentication into security frameworks helps organizations implement stronger identity verification.
Companies can use facial recognition technology for:
-
Secure login to corporate systems
-
Identity verification for remote employees
-
Restricted access to sensitive data
-
Device authentication for company laptops and mobile devices
By replacing traditional login methods, businesses significantly reduce unauthorized access risks.
Strengthening Digital Investigations with eInvestigator
Modern security frameworks often combine biometric verification with advanced monitoring solutions. Tools like eInvestigator help organizations analyze user activity and detect suspicious behavior across digital environments.
When combined with facial authentication, eInvestigator enables organizations to:
-
Track verified user sessions
-
Maintain accurate audit logs
-
Investigate unusual system activity
-
Strengthen compliance reporting
This integration ensures that every system interaction is linked to a verified identity, improving accountability across the organization.
Preventing Insider Threats with Biometric Security
One of the biggest cybersecurity risks today comes from within the organization. Employees or contractors with system access can unintentionally or intentionally expose sensitive data. Insider Threat Prevention strategies increasingly rely on biometric technologies like Facial Authentication.
Facial authentication supports insider threat prevention by:
-
Verifying user identity before granting system access
-
Preventing unauthorized device usage
-
Detecting suspicious login attempts
-
Creating reliable identity logs for investigations
By linking user actions to biometric identity verification, organizations gain stronger protection against internal security risks.
Best Practices for Implementing Facial Authentication
To maximize the effectiveness of facial authentication systems, businesses should follow a structured implementation strategy.
Recommended best practices:
-
Combine facial authentication with multi-factor authentication (MFA)
-
Use encrypted storage for biometric data
-
Conduct regular security audits and updates
-
Implement monitoring tools like eInvestigator for activity tracking
-
Train employees on biometric security policies
Following these practices helps organizations maintain both security and privacy.
The Future of Facial Authentication in the Workplace
As digital transformation accelerates, biometric technologies are becoming essential components of enterprise security. Facial Authentication will likely play an even larger role in identity verification, remote workforce security, and fraud prevention.
Future advancements may include:
-
AI-driven facial recognition improvements
-
Integration with smart access control systems
-
Real-time behavioral analysis for security monitoring
-
Expanded use in remote and hybrid workplaces
Organizations that adopt biometric authentication today are better positioned to protect their digital infrastructure tomorrow.
Conclusion
Facial Authentication is transforming how organizations verify identity and secure access to critical systems. By replacing traditional passwords with biometric verification, businesses can significantly reduce unauthorized access risks and improve operational efficiency.
When combined with advanced monitoring tools like eInvestigator and strong Insider Threat Prevention strategies, facial authentication creates a powerful security framework that protects both digital assets and organizational integrity.
If you’re looking to enhance workforce security and gain deeper visibility into user activity, the right platform can make all the difference.
Secure Your Workforce and Systems Today
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Παιχνίδια
- Gardening
- Health
- Κεντρική Σελίδα
- Literature
- Music
- Networking
- άλλο
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness


